What is Two-factor Authentication (2FA)?
Two-factor authentication is designed to be an additional layer of security between the user and the account. This means that if someone has your username and password, they will not immediately gain access to your account - they will also need to pass another stronger security measure.
Why use two-factor authentication?
Adding two-factor authentication to your account is a quick and easy method of increasing your account security. Every week a new story appears about how government institutions and large corporations accounts are hacked or compromised. The most notable breach for the UK was the NHS hack in 2017.
According to a recent report, the most common breaches involve small businesses:
- 43% of breaches involve small businesses
- 32% of breaches involved phishing
- 29% of breaches used stolen credentials
- 39% of breaches were conducted by organised criminal groups
Other statistics indicate that mobile users are more susceptible to phishing attempts. This is likely due to the constraints on screen space and features, where providers are more likely to show less information to mobile users in order to provide a "better experience".
With 2FA enabled, your account is better protected against phishing attempts, scripted attacks and more.
The three methods of authentication
To identify and authenticate users, authentication must meet two or more of the following criteria:
- Something you know (password or pin)
- Something you have (app-based or hardware)
- Something you are (fingerprint or facial recognition)
You are usually identified by your username and authenticated via your password. The additional security method(s) ensure that providers are further able to authenticate your identity.
Common methods of authentication and misconceptions
The method of 2FA that you will likely be most familiar with is your chip and pin device for online banking. This is hardware-based authentication and falls under the "something you have" method.
It works by combining "something you know", such as your debit card number or sort code and account number, with a hardware-based token. This token is generated when you insert your debit card into the chip and pin device and pass the authentication.
The most common online methods of authentication are SMS/Email authentication and app-based authentication. It is important to note that SMS/Email and app-based authentication achieve the same goal, but they are not the same.
SMS & Email (2SV)
App & Hardware (2FA)
Biometrics (2FA/3FA)
SMS and Email based authentication are considered 2-step verification. Whereas app-based authentication can be considered 2FA. This is down to 2-step verification not meeting 2 of the 3 authentication criteria required for 2FA.
The first step is your password, which is "something you know". The second step requires either "something you have" or "something you are". The misconception is that many believe your device is "something you have", whereas from a security standpoint it actually falls under "something you know".
This is because the device doesn't authenticate your login'information on the device is used in the authentication process.
2-step verification is still strong enough to deter most non-authenticated users but it's strongly recommended that you employ either 2FA or 3FA security to your accounts where possible.
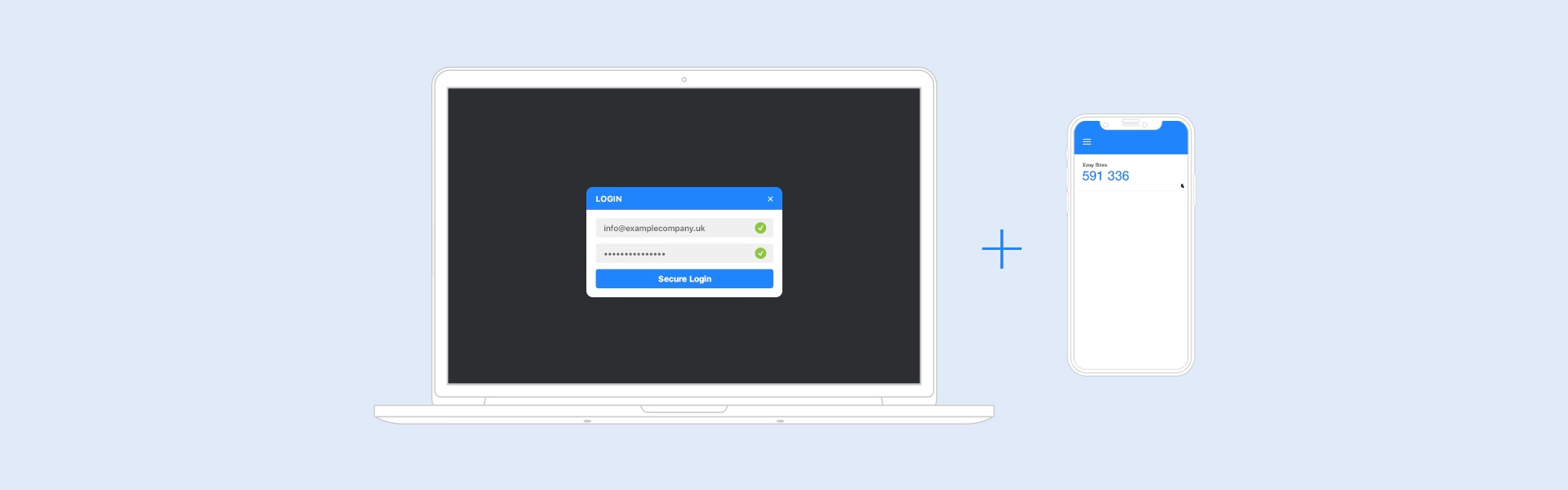
2FA and Easy Sites
Protecting your website is paramount for your business. Our content management system (CMS) allows you to enable 2FA for your account quickly and easily. If you haven't enabled 2FA in your Easy Sites account, you can follow our guide on How to Enable 2FA in Easy Sites.
If you have any additional questions about two-factor authentication or any of our products and services, please simply contact us via 01253 968004 or complete our email contact form.